Cyber Resilience Act for IoT: 2026 Compliance Roadmap
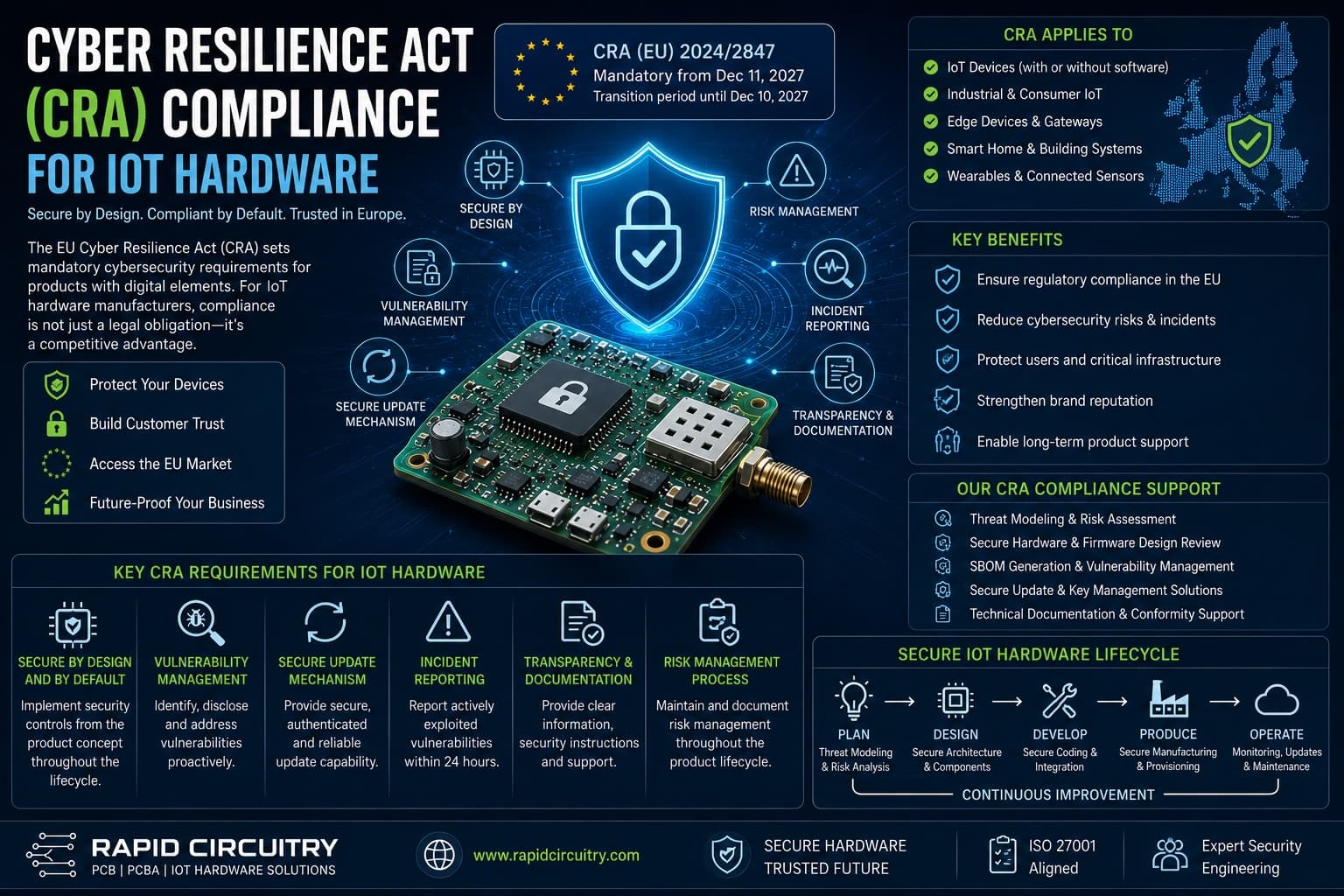
The Cyber Resilience Act (CRA) is now in force across the EU, and any product with digital elements placed on the European market after December 11, 2027 must meet its essential cybersecurity requirements. For hardware teams shipping connected devices, 2026 is the year to translate the regulation into design decisions, documentation, and supply-chain processes. This guide breaks down what the Cyber Resilience Act demands from hardware teams and lays out a 2026 roadmap for CE conformity.
Key Takeaways
- The Cyber Resilience Act applies to nearly any product with digital elements placed on the EU market, including most IoT devices, gateways, microcontrollers shipped with firmware, and embedded modules.
- Vulnerability reporting and incident notification obligations apply from September 11, 2026; the full set of essential requirements applies from December 11, 2027.
- Most IoT hardware lands in the default category and can use self-assessment, but Important Class II and Critical products require third-party conformity assessment by a notified body.
- Hardware teams must implement secure boot, signed firmware updates, debug lockout, and a documented vulnerability handling process at the device level, with a declared support period of at least five years in most cases.
- An SBOM in CycloneDX or SPDX format covering firmware, bootloaders, and bundled libraries is part of the CRA technical documentation.
- Penalties for non-compliance with essential requirements reach EUR 15 million or 2.5% of global annual turnover, whichever is higher.
What the Cyber Resilience Act Requires from Hardware Teams
The Cyber Resilience Act is the EU's first horizontal cybersecurity regulation for products with digital elements. Unlike NIS2, which targets organizations and critical infrastructure operators, the Cyber Resilience Act targets products themselves — anything with software or firmware that connects directly or indirectly to a network or another device. For most hardware engineers reading this, that scope captures everything from a Wi-Fi enabled sensor to a managed industrial gateway.
Scope and Definition of Products with Digital Elements
The regulation defines a product with digital elements as any software or hardware product whose remote data processing solutions are integral to its function. In practice, that includes microcontrollers shipped with bundled firmware, BLE and Wi-Fi modules, smart sensors, residential gateways, industrial PLCs, and consumer wearables. Hardware-only products with no firmware are out of scope, but increasingly rare in IoT — even a basic sensor with an on-board ADC usually ships with vendor firmware that pulls it back into scope.
Importers and distributors share responsibility with manufacturers. If a contract manufacturer in Asia builds finished hardware for an EU brand owner, the EU brand owner bears the manufacturer obligations as the legal placer-on-the-market.
The Annex I Essential Requirements
Annex I of the CRA defines two sets of requirements: a baseline of cybersecurity properties the product must have, and a set of vulnerability handling process requirements the manufacturer must run for the duration of the support period. Hardware-relevant items in the product properties set include a secure-by-default configuration, protection against unauthorized access through appropriate authentication and access controls, confidentiality and integrity of data at rest and in transit, minimization of attack surface and external interfaces, and the ability to apply security updates including automatic updates where appropriate.
Concretely, this maps to design decisions like enabling secure boot on the application MCU, disabling JTAG and SWD on production builds, encrypting data at rest on flash, supporting authenticated firmware updates, and shipping with no default credentials. Many of these were already engineering best practice for any team taking IoT security seriously, but the Cyber Resilience Act turns them into legal obligations rather than recommendations.
Vulnerability Handling Process Requirements
Beyond product properties, the regulation imposes ongoing process obligations on manufacturers. You must identify and document vulnerabilities and components in the product, address them in a timely manner with security updates, perform regular tests, share information about fixed vulnerabilities, run a coordinated vulnerability disclosure (CVD) policy, and provide a contact address for vulnerability reports. The support period during which these obligations apply is at least five years, or the expected use period of the product if shorter, and you must document and communicate that period to users at the point of purchase.
For startups and smaller OEMs, this is often the harder lift. Designing secure boot into a board is a one-time engineering effort; running a CVD process and shipping signed updates for five years is an operational commitment that needs budgeting from day one.
Conformity Assessment Routes and Product Classes
The Cyber Resilience Act splits products into four conformity assessment categories, and the route a manufacturer takes depends on what the product does, not where it ships from.
| Class | Examples (illustrative) | Conformity Assessment | Notes |
|---|---|---|---|
| Default | Smart sensors, consumer wearables, smart bulbs, fitness trackers | Self-assessment (Module A) | Manufacturer applies the CRA requirements internally and self-declares conformity |
| Important Class I | Password managers, network management systems, microcontrollers with security functions, smart home assistants | Self-assessment using harmonized standards, or third-party assessment | Self-assessment allowed only when harmonized standards are fully applied |
| Important Class II | Hypervisors, firewalls, tamper-resistant microprocessors, hardware security modules for general use | Third-party conformity assessment required | Notified body involvement is mandatory |
| Critical | Smart meter gateways, hardware devices with security boxes, smart cards used in critical infrastructure | EU cybersecurity certification under the Cybersecurity Act, when available | Highest scrutiny; certification under EU schemes such as EUCC may apply |
Most off-the-shelf IoT devices land in the default category, which means a hardware team can complete the conformity assessment internally as long as they document it. The trap is misclassifying an Important Class I product — for example a microcontroller marketed with security features — as default. Notified bodies and market surveillance authorities can challenge classification, and an incorrect self-declaration is itself a Cyber Resilience Act violation.
Hardware Design Implications for CRA Compliance
Because the regulation is technology-neutral, it does not mandate specific implementations. The essential requirements still push design teams toward a fairly consistent set of hardware choices that should land in the schematic and stackup, not be retrofitted at the end of layout.
Secure Boot, Root of Trust, and Update Authentication
A modern IoT product needs an immutable root of trust, typically anchored in MCU mask ROM or a one-time-programmable region, that verifies the bootloader, which in turn verifies the application image. Most current-generation MCUs from STMicroelectronics, NXP, Nordic, Silicon Labs, Renesas, and Espressif support secure boot in some form, but enabling it correctly during production programming is a separate engineering and DFM exercise. Boards routinely ship with secure boot disabled because nobody turned it on at the programming station.
Authenticated firmware updates are the second hard requirement. The image must be signed with a key the bootloader can verify, and the verification step must precede flash erase to prevent bricking on a bad image. Most MCUs support ECDSA over P-256 or RSA-2048 in the bootloader; the choice affects flash footprint and verification time, neither of which matters much on a Cortex-M33 but matters a lot on a Cortex-M0+.
Hardware Anti-Tamper and Debug Lockout
The Cyber Resilience Act's protection-against-unauthorized-access requirement effectively rules out leaving JTAG and SWD enabled on shipping units. Production firmware should program the readout protection or debug lock fuse, and the PCB should not expose programming pads on accessible test points. For higher-assurance products, anti-tamper switches, secure enclosures, or active mesh sensing can detect physical intrusion and trigger key zeroization in the secure element.
Cryptographic Co-processors and Secure Elements
Storing identity keys in MCU flash is acceptable for default-class products, but increasingly inadequate for Important products and certainly for Critical ones. Secure elements such as the Microchip ATECC608B, NXP EdgeLock SE05x, and Infineon OPTIGA Trust M provide hardware-isolated key storage, and TPM-class devices add measured boot. Adding a secure element costs board space, BOM dollars, and a few extra I2C lines, but it simplifies the conformity-assessment argument that keys cannot be extracted by software attacks. The trade-off is one our team often weighs early in PCB design and prototyping engagements.
SBOM and the Cyber Resilience Act 2026 Timeline
The CRA technical documentation is more comprehensive than the typical CE technical file under, say, the EMC or Radio Equipment directives. It must include a description of the product design, development, and production, an assessment of cybersecurity risks, evidence the essential requirements are met, the SBOM, and details of the vulnerability handling process.
Building an SBOM Across the Hardware-Software Boundary
An SBOM lists all software components included in the product, with names, versions, suppliers, and cryptographic hashes where available. SPDX and CycloneDX are the dominant interchange formats; CycloneDX has stronger support for firmware-specific use cases including bundled bootloaders, RTOS components, and pre-built libraries. The SBOM has to cover everything that ends up in the device — vendor BSPs, third-party drivers, MQTT and TLS libraries, HAL code from the silicon vendor, and any open-source components linked into the firmware image. For RTOS-based designs, that often means hundreds of items; for Yocto-based Linux IoT devices, several thousand.
The SBOM is also where supply chain attacks and CVEs intersect with regulatory obligations. When a vulnerability is disclosed in a library, the SBOM tells you whether it is in your product, the vulnerability handling process tells you how fast you must respond, and the technical file demonstrates to a market surveillance authority that you knew what you shipped.
Key 2026 Milestones for Hardware Teams
The Cyber Resilience Act's transitional periods are short relative to the typical hardware product development cycle, which is precisely why 2026 is the planning year.
| Date | What changes | What hardware teams should do |
|---|---|---|
| December 10, 2024 | CRA entered into force | Already passed; obligations triggered for new development cycles |
| September 11, 2026 | Vulnerability reporting and incident notification obligations apply | Stand up a CVD policy, an actively monitored vulnerability inbox, and incident reporting workflows to ENISA and national CSIRTs |
| December 11, 2027 | Full application of essential and conformity assessment requirements; CE marking covers CRA | All new products placed on the EU market must comply |
Products already on the EU market before December 2027 are not retroactively covered unless they undergo substantial modifications, which any new firmware release adding new functionality typically counts as. Plan platform refreshes accordingly.
External authoritative reading on the regulation includes the official EUR-Lex regulation text and the ENISA topic page on the Cyber Resilience Act. For an aligned hardware security standard, IEC 62443-4-2 provides component-level security requirements that map well to Annex I.
Practical Implications for Hardware Teams
Translating the regulation into engineering tasks for a 2026 development cycle:
- Audit the current IoT product portfolio and classify each SKU as default, Important Class I, Important Class II, or Critical. Document the classification rationale in the technical file.
- Add secure boot, signed updates, and debug lockout to the DFM checklist for any new board spin shipping into the EU after December 2027.
- Choose silicon partners that publish long-term-support roadmaps matching or exceeding the declared CRA support period, typically five years or longer.
- Stand up an SBOM generation pipeline integrated into CI that emits CycloneDX or SPDX from every firmware build, including the bootloader and any pre-built binaries.
- Set up a security inbox, a coordinated vulnerability disclosure policy, and an incident playbook before September 11, 2026.
- Budget for a five-year minimum security update commitment per shipping product, including someone to triage CVEs against the SBOM and ship signed update packages.
- For products that may classify as Important or Critical, identify a notified body early and factor third-party assessment timelines into the launch plan.
- Talk to the contract manufacturer about secure programming, key injection at the production line, and traceability of programmed devices back to a signed manufacturing record.
Common Questions About the Cyber Resilience Act
When does the Cyber Resilience Act take effect?
The Cyber Resilience Act entered into force on December 10, 2024. Vulnerability reporting and incident notification obligations apply from September 11, 2026, and the full set of essential and conformity assessment requirements applies from December 11, 2027.
Does the CRA apply to products sold outside the EU?
The regulation only governs products placed on the EU market. A device sold exclusively in North America or Asia is out of scope. However, most hardware OEMs build a single global SKU, so CRA compliance effectively becomes the floor for the worldwide product to avoid maintaining two firmware variants.
What's the difference between Important Class I and Class II products?
Class I includes products with security-relevant functions where harmonized standards generally exist, allowing self-assessment if those standards are fully applied — examples include microcontrollers with security functions and smart home assistants. Class II includes higher-risk products such as firewalls, hypervisors, and tamper-resistant microprocessors, where third-party assessment by a notified body is mandatory regardless of which standards are used.
Do hardware-only devices need an SBOM?
If the device contains any software or firmware — including vendor-provided MCU firmware, an FPGA bitstream with embedded soft cores, or a bundled BLE stack — then yes. Truly software-free products are out of CRA scope entirely, but in IoT they are vanishingly rare.
Can a microcontroller vendor's CRA compliance cover my finished product?
No. The MCU vendor's obligations cover the chip and its bundled firmware as placed on the EU market. The finished-product manufacturer assumes its own obligations for the integrated device. Vendor compliance helps in practice — for example, a vendor secure-boot implementation reduces in-house engineering work — but it does not transfer.
What are the penalties for non-compliance?
Non-compliance with the essential cybersecurity requirements or the manufacturer obligations can be fined up to EUR 15 million or 2.5% of total worldwide annual turnover for the preceding financial year, whichever is higher. Other breaches carry lower ceilings of EUR 10 million or 2% turnover, and EUR 5 million or 1% turnover for false or incomplete information supplied to notified bodies and market surveillance authorities.
Working With Rapid Circuitry on CRA-Ready Hardware
Cyber Resilience Act compliance is a hardware-software co-design problem, not a checkbox to tick at the end of layout. Anchoring secure boot, key provisioning, anti-tamper, and DFM-friendly programming into the schematic and stackup early avoids painful redesigns close to launch. Rapid Circuitry works with hardware teams on PCB design, prototyping, and manufacturing for connected products, and the team can help structure secure boot enablement, SBOM-aware firmware build flows, and production programming for CE marking aligned with the regulation. If you are scoping a 2026 design refresh against the CRA timeline, get in touch with the team to walk through the hardware design implications for your specific product class. For deeper coverage of the underlying secure boot and root-of-trust techniques, see our Secure Boot and Hardware Security for IoT in 2026 guide.
Need help with secure hardware & cybersecurity?
Get a free consultation with our expert engineers. We respond within 24 hours.
Get a Free ConsultationStay in the Loop
Subscribe to our newsletter for the latest updates and insights.
By subscribing, you agree to our Privacy Policy. You can unsubscribe at any time.